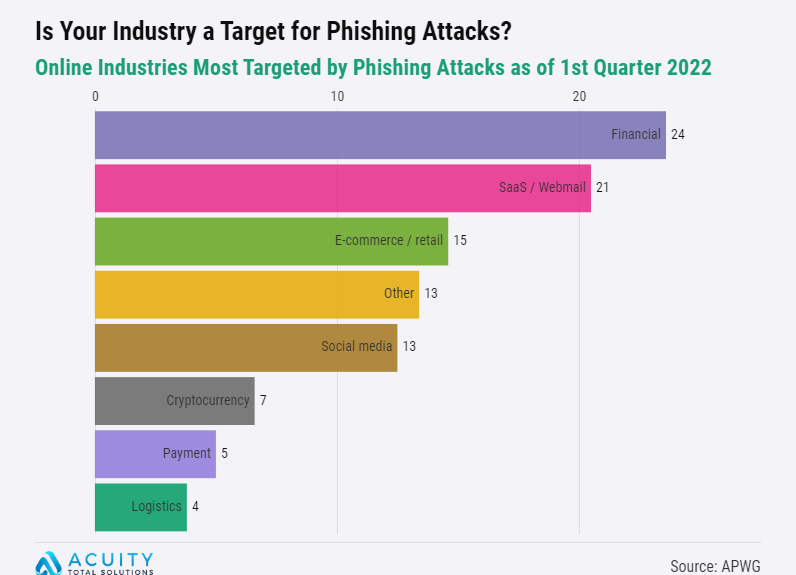
Online Industries Most Targeted by Phishing Attacks as of 1st Quarter 2022
A recent report released by the Anti-Phishing Working Group (APWG) reveals “an all time high” in online Phishing attacks.
Phishing is a scam that attempts to lure victims into giving up their usernames, passwords, or other sensitive information. This is done by a criminal masquerading as someone they know and trust. This is typically done by email, but can also be done by phone.
The APWG report details the percentage of online industries most often targeted by scammers. You can download an infographic here:
“Human error is the greatest ongoing threat to a company’s security. Training is essential to prepare and maintain awareness of these attacks. As they say, an ounce of prevention is worth a pound of cure.” – Esther Maria Chamberlain, President, Acuity Total Solutions
Types of Phishing Attacks:
1. Email phishing
Most phishing attacks are received via email. Scammers often register fake domains that mimic genuine organizations. They then send thousands of emails to “Phish.”
2. Spear phishing
A more sophisticated type of phishing email, spear phishing is a malicious email sent to a specific person. Criminals who do this will already have a considerable amount of information about the target. This often includes their full name, job role, and other personal details that make the email more convincing.
3. Whaling
Whaling attacks are even more specific, taking aim at senior executives and management roles. Although whaling has the same goal as any other kind of phishing attack, the technique can be more subtle. This can require more specific training for high-level staff.
4. Smishing and vishing
Smishing and vishing refers to telephones, instead of emails, as the method of communication.
Smishing involves text messaging content that is similar to email phishing, and vishing involves telephone conversation.
A common smishing text is a message claiming to come from the target’s bank.
5. Angler phishing
A scam born of social media, angler phishing employs the various communication tools offered on social platforms. Fake URLs and profiles, posts, tweets, and instant messaging can all be used to coax people to share sensitive information or download malware.
Is your industry at risk?
Acuity Total Solutions provides complete facility services from IT and Cyber Security to landscaping and custodial.
For more information or to interview Esther, please feel free to contact us.