As digital security breaches continue to increase around the world, organizations large and small have fallen victim to coordinated and costly cyber-attacks. Ransomware attacks, for example, have risen by 13% in 2022 according to Verizon. Ransomware attacks use malware to take control of a company’s data and permanently block access to it unless a ransom is paid. These ransoms can cost companies tens of thousands, sometimes hundreds of thousands of dollars, to resume doing business.
This growing threat demands a practical and deliberate plan to protect a company’s systems. This article will outline 5 foundational steps that are needed to build a dependable security framework.
1. Create and Fill a Security Program Manager Role
A Security Program Manager is a dedicated employee tasked with ensuring that your organization implements all the key elements of a strong cybersecurity program. The manager should help create a culture of security awareness and best practices, provide monthly reports on progress and threats, and create an Incident Response Plan (IRP) to practice and implement in the event of a security threat.
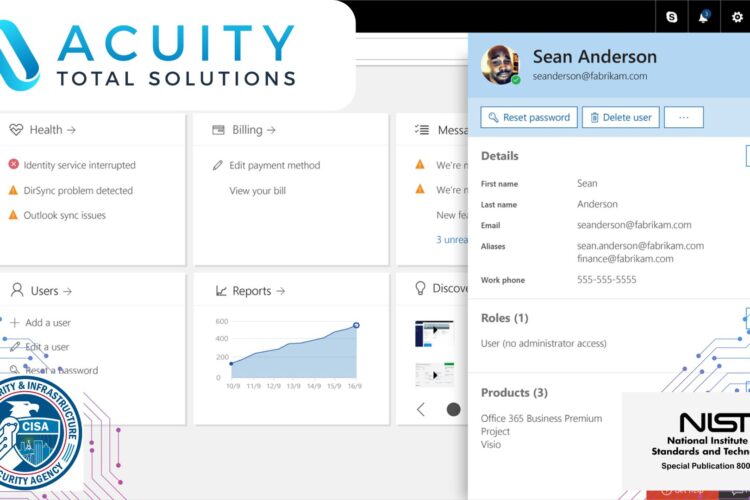
2. Establish Multi-Factor Authentication (MFA)
MFA is an authentication method that requires a user to provide two or more verification factors to gain access to a resource such as an application, online account or website. MFA is the most important step an organization can take to protect their systems from attack, especially email. This second form of verification provides a confirmation level of security in the event of a compromised password. The most common example of MFA is password access verified by a verification code sent to a user’s phone. MFA’s can include a secondary Personal Identification Number (PIN), cryptographic identification devices or tokens, biometric authenticators, and FIDO authentication.
Without exception, MFA should be enabled for all system administrator accounts. IT leads and Security Program Managers. Because admin accounts can allow unrestricted access to a company’s assets and are often the main target of attackers, managers should verify that all admin accounts are protected.
3. Employee Training for Cyber Security
The role of human error in security breaches cannot be understated. Training is a key element to ensure employees practice good security habits on a daily basis. The Security Program Manager should hold quarterly meetings to review common and emerging attacks and to reinforce previous training. This is also a good time to review IRPs to discuss close calls or other security incidents. Tabletop exercises are a great way to present common security scenarios that employees may face.
4. The IT Lead in Cyber Security
The IT Lead plays an important role in supporting the efforts of the Security Program Manager. While the support tasks can vary, the key basics include maintaining the latest in software patches and ensuring MFA compliance.
IT professionals can also regularly perform and test system backups. In the event of a ransomware attack, for instance, a tested and current backup can provide the needed solution. Regularly testing partial and full restores, and having an official restoration plan, can ensure quick and successful system restores that minimize the negative impact on business.
Removing administrator access and enabling disk encryption on user laptops can protect against malicious software installs and data taken from stolen devices.
5. Move Data to the Cloud
While no data system will be 100% secure, companies can greatly minimize their risk by reducing the number of services that they host on the premises. The time and cost commitment needed to secure, maintain, and monitor hosted email and file storage can be significantly decreased by migrating to cloud services.
These services are maintained by the best engineers and security experts in the world, while often reducing the overall cost to the company.
Another benefit of cloud services is the ability to secure endpoints. Devices like iPads and Chromebooks are secure by design – any data is stored on a secure cloud service, reducing the damage done in the event of an attack. Many companies have migrated to these devices to reduce their security risk.
Basic Steps to Cyber Security
While this list of needs is by no means exhaustive, these steps can greatly contribute to a secure data environment for any business. The risk of a data breach, a ransomware attack, or a complete failure of a company’s systems are too great to ignore. And as cybercrime increases, it is essential for any company to implement security best practices.
Acuity Total Solutions provides full-service IT and Security services for organizations of all sizes.