Cyberattacks are on the rise. Internet-connected systems must be protected from these threats by utilizing cybersecurity practices used by individuals and enterprises.
A strong cybersecurity strategy can defend against malicious attacks and prevent them from accessing, altering, deleting, destroying, and extorting your organization or user’s system. Cybersecurity also prevents attacks that aim to disable or disrupt a system’s operations.
Practicing Proper Cybersecurity
With the increase in usage of connected devices and programs, combined with the increased deluge of data (which is sensitive or confidential) the importance of cybersecurity continues to grow. With more IT assets being fostered and new attack techniques being created, it becomes increasingly difficult for IT teams to keep pace.
With many different kinds of threats being presented, it is important to adopt a more proactive, adaptive approach. The balance between reactive and proactive models is important because many known and unknown threats exist.
Cybersecurity methodologies are used to protect a company from cyberattacks, data breaches, and unauthorized user access. Various types of cybersecurity attacks include ransomware, spyware, phishing scams, botnets, backdoors, malware.
Keeping up with new technologies, security trends and other threats is, in many ways, a time consuming endeavor. It’s necessary, however, in order to protect information and other assets from cyberthreats that can take many forms.
The most common cyberthreats include:
Malware. Malware is any kind of software that is harmful to a computer. This includes worms, viruses, Trojans and spyware.
Ransomware. The type of malware that asks for ransom in order to unlock files from encryption is called ransomware.
Social engineering. Social engineering attacks rely on human interaction to trick an individual into giving up their passwords or sensitive data.
Phishing. Phishing emails are the most common form of social engineering attack, where a fraudulent url will appear as if it is from a reputable source like Facebook or Tumblr.
Spear phishing. Spear phishing goes after specific targets rather than going for mass email addresses.
Insider threats. Insider threats can be malicious or inadvertent in nature; commonly because employees, contractors or customers contribute to the problem.
DDOS. Distributed denial-of-service (DDoS) attacks involve multiple systems crashing or incapacitating one central apparatus; preventing any legitimate traffic from passing through it.
APT. Advanced persistent threats (APT) are prolonged targeted attacks that consist of long term penetration with the goal of stealing information.
MitM. Man in the Middle (MitM) attacks use an attacker in lieu of two parties who otherwise would legitimately communicate with each other with no eavesdropper present.
Other forms of common malware include botnets, drive-by downloads, exploit kits and vishing.
Constantly Changing Threat Environments
Cybersecurity is continually challenged by hackers, data loss, privacy and more. As new ways of being hacked come in with the Internet of Things (IoT), it’s clear that the need for cybersecurity will only grow.
For cyber-security there is always a new risk that comes to light. Keeping up with these changes can be difficult for organizations due to the possibility of vulnerabilities in their system and lack of resources. They need to make sure they are well protected against any vulnerabilities.
It’s important to educate employees by providing them with security awareness training as they may unintentionally bring viruses into the workplace. Cybersecurity programs should also have an employee education component that incorporates continual training, both at-work and over the internet.
It’s difficult to find qualified cybersecurity staff due to an increasing number of job openings. As companies collect and use more data, there is a growing need for professionals with the occupation to monitor and address incidents. Experts estimate that there is a 3.1 million person gap between jobs needed in cybersecurity and professional security workers in the field.
What automation can be used in cybersecurity?
Companies can protect themselves against cybersecurity threats using AI that has become a mainstay in the modernized world.
Automation in security prevents threats by recognizing known cybersecurity threats and predicting novel ones. Human augmentation includes automating repetitive tasks and triaging low-risk alarms to free up security professionals to deal with more sophisticated tasks.
To protect your network from cybersecurity threats, you need a multi-layered defense.
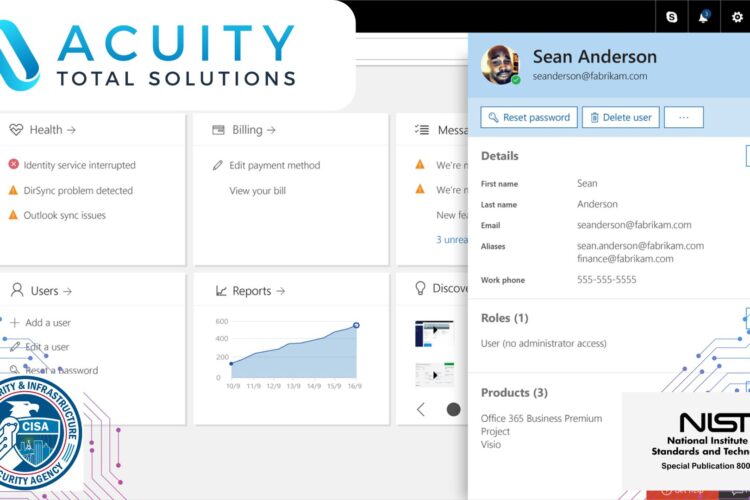
Acuity Total Solutions provides IT infrastructure and cyber security services, in order to protect your business from data security breaches, ransomware attacks, and other cyber threats.